You can grant read/write access for individual Azure storage (V1 or V2) containers (e.g. a Blob storage container) to Azure active directory users: Let us say we want the user testuser@mydomain.onmicrosoft.com have merely read access to the (private) container auditinfoclient01. To accomplish this, just choose the container in the Azure portal and open the Access Control blade:
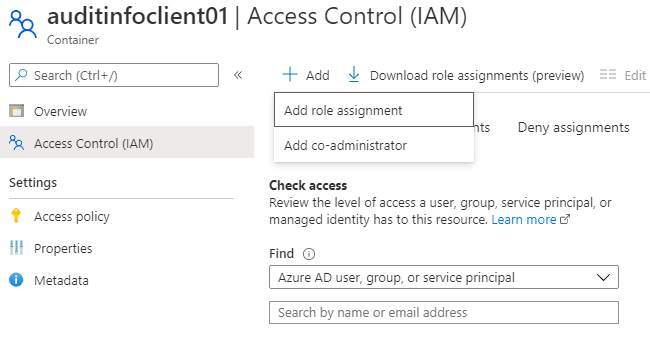
Add a role assignment for the testuser as “Storage Blob Data Reader“:

The user have now access to this container in a read-only manner. But it is not enough! If testuser@mydomain.onmicrosoft.com has no access to the storage account itself (directly or through inheritance, e.g. from the resource group), then she/he will not be able to access the container using the Azure portal, nor using the Microsoft Azure Storage Explorer. The storage account will not be visible to her/him. To fix this, we have to assign her/him a “reader” role on the corresponding storage account:

This guarantees that after successful (re) login to the Azure portal, our testuser can see the storage account, and can read the content of auditinfoclient01 container. She/He can see the list off all containers under this storage account, but if she/he tries to open one of them (other than auditinfoclient01) she/he get an unauthorized error:

Trying to get the access keys is not possible either, as expected:

Hope this is useful to someone!